* [FEATURE] File Secret Loading * add a validator for secrets * run the secrets validator before the main config validator * only allow a secret to be defined in one of: config, env, file env * remove LF if found in file * update configuration before main config validation * fix unit tests * implement secret testing * refactor the secrets validator * make check os agnostic * update docs * add warning when user attempts to use ENV instead of ENV file * discourage ENV in docs * update config template * oxford comma * apply suggestions from code review * rename Validate to ValidateConfiguration * add k8s example * add deprecation notice in docs and warning * style changes |
||
|---|---|---|
| .buildkite | ||
| .dependabot | ||
| .github | ||
| cmd | ||
| compose | ||
| docs | ||
| internal | ||
| web | ||
| .dockerignore | ||
| .gitignore | ||
| .golangci.yml | ||
| .reviewdog.yml | ||
| BREAKING.md | ||
| CONTRIBUTING.md | ||
| Dockerfile | ||
| Dockerfile.arm32v7 | ||
| Dockerfile.arm64v8 | ||
| Dockerfile.darwin | ||
| LICENSE | ||
| README.md | ||
| authelia.service | ||
| bootstrap.sh | ||
| config.template.yml | ||
| go.mod | ||
| go.sum | ||
README.md

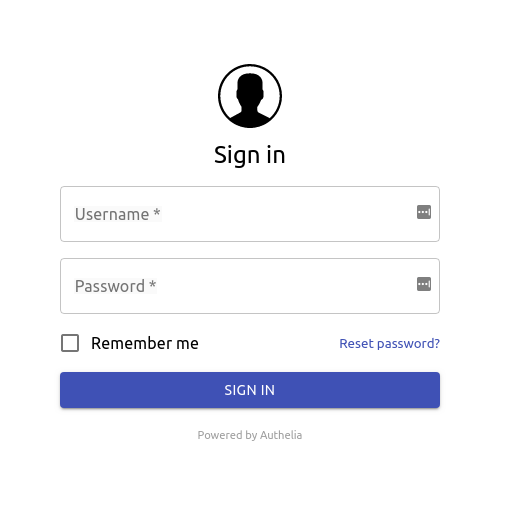
Authelia is an open-source authentication and authorization server providing 2-factor authentication and single sign-on (SSO) for your applications via a web portal. It acts as a companion of reverse proxies like nginx, Traefik or HAProxy to let them know whether queries should pass through. Unauthenticated user are redirected to Authelia Sign-in portal instead.
Documentation is available at https://docs.authelia.com.
The architecture is shown in the diagram below.

Authelia can be installed as a standalone service from the AUR, using a Static binary, Docker or can also be deployed easily on Kubernetes leveraging ingress controllers and ingress configuration.


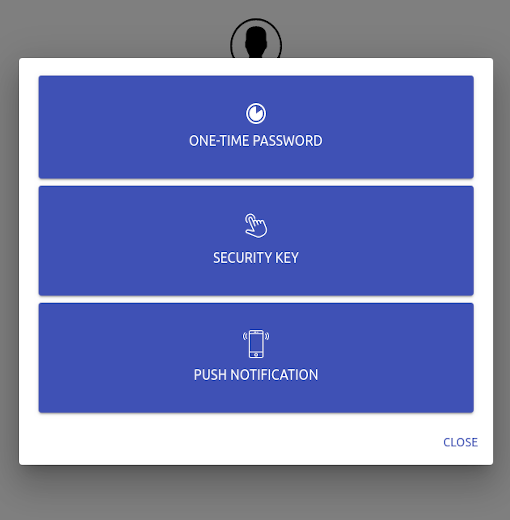
Here is what Authelia's portal looks like
Features summary
Here is the list of the main available features:
- Several kind of second factor:
- Password reset with identity verification using email confirmation.
- Single-factor only authentication method available.
- Access restriction after too many authentication attempts.
- Fine-grained access control per subdomain, user, resource and network.
- Support of basic authentication for endpoints protected by single factor.
- Highly available using a remote database and Redis as a highly available KV store.
- Compatible with Kubernetes ingress-nginx controller out of the box.
For more details about the features, follow Features.
Proxy support
Authelia works in combination with nginx, Traefik or HAProxy. It can be deployed on bare metal with Docker or on top of Kubernetes.




Getting Started
You can start utilising Authelia with the provided docker-compose bundles:
Local
The Local compose bundle is intended to test Authelia without worrying about configuration. It's meant to be used for scenarios where the server is not be exposed to the internet. Domains will be defined in the local hosts file and self-signed certificates will be utilised.
Lite
The Lite compose bundle is intended for scenarios where the server will be exposed to the internet, domains and DNS will need to be setup accordingly and certificates will be generated through LetsEncrypt. The Lite element refers to minimal external dependencies; File based user storage, SQLite based configuration storage. In this configuration, the service will not scale well.
Full
The Full compose bundle is intended for scenarios where the server will be exposed to the internet, domains and DNS will need to be setup accordingly and certificates will be generated through LetsEncrypt. The Full element refers to a scalable setup which includes external dependencies; LDAP based user storage, Database based configuration storage (MariaDB, MySQL or Postgres).
Deployment
Now that you have tested Authelia and you want to try it out in your own infrastructure, you can learn how to deploy and use it with Deployment. This guide will show you how to deploy it on bare metal as well as on Kubernetes.
Security
Security is taken very seriously here, therefore we follow the rule of responsible disclosure and we encourage you to do so.
Would you like to report any vulnerability discovered in Authelia, please first contact clems4ever on Matrix or by email.
For details about security measures implemented in Authelia, please follow this link.
Breaking changes
See BREAKING.
Contribute
If you want to contribute to Authelia, check the documentation available here.
Contributors
Authelia exists thanks to all the people who contribute. [Contribute].
Backers
Thank you to all our backers! 🙏 [Become a backer] and help us sustain our community.
Sponsors
Support Authelia by becoming a sponsor. Your logo will show up here with a link to your website. [Become a sponsor]
License
Authelia is licensed under the Apache 2.0 license. The terms of the license are detailed in LICENSE.









