Bumps [@material-ui/core](https://github.com/mui-org/material-ui/tree/HEAD/packages/material-ui) from 4.10.0 to 4.10.1. - [Release notes](https://github.com/mui-org/material-ui/releases) - [Changelog](https://github.com/mui-org/material-ui/blob/master/CHANGELOG.md) - [Commits](https://github.com/mui-org/material-ui/commits/v4.10.1/packages/material-ui) Signed-off-by: dependabot-preview[bot] <support@dependabot.com> Co-authored-by: dependabot-preview[bot] <27856297+dependabot-preview[bot]@users.noreply.github.com> |
||
|---|---|---|
| .buildkite | ||
| .dependabot | ||
| .github | ||
| cmd | ||
| compose | ||
| docs | ||
| internal | ||
| web | ||
| .dockerignore | ||
| .gitignore | ||
| .golangci.yml | ||
| .reviewdog.yml | ||
| BREAKING.md | ||
| CONTRIBUTING.md | ||
| Dockerfile | ||
| Dockerfile.arm32v7 | ||
| Dockerfile.arm64v8 | ||
| LICENSE | ||
| README.md | ||
| SECURITY.md | ||
| authelia.service | ||
| bootstrap.sh | ||
| config.template.yml | ||
| go.mod | ||
| go.sum | ||
README.md

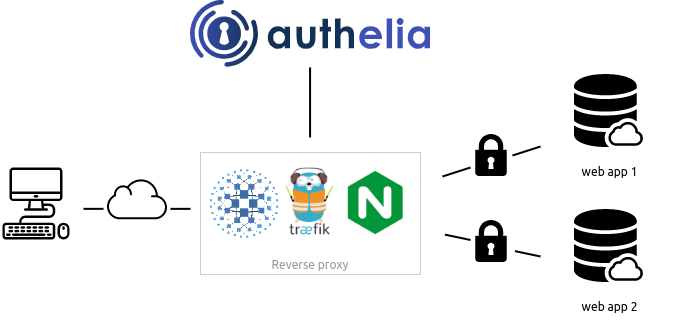
Authelia is an open-source authentication and authorization server providing 2-factor authentication and single sign-on (SSO) for your applications via a web portal. It acts as a companion of reverse proxies like nginx, Traefik or HAProxy to let them know whether queries should pass through. Unauthenticated user are redirected to Authelia Sign-in portal instead.
Documentation is available at https://docs.authelia.com.
The architecture is shown in the diagram below.
Authelia can be installed as a standalone service from the AUR, using a Static binary, Docker or can also be deployed easily on Kubernetes leveraging ingress controllers and ingress configuration.

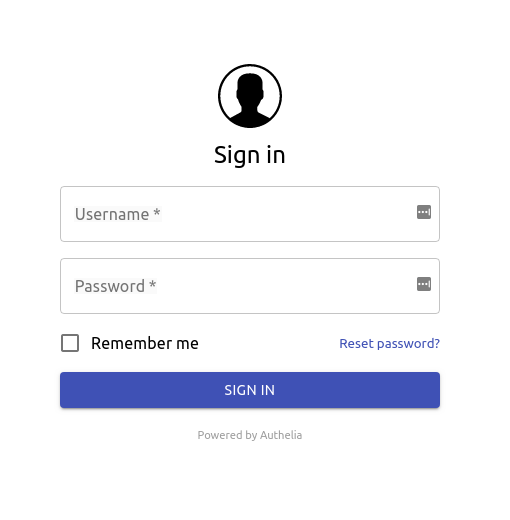
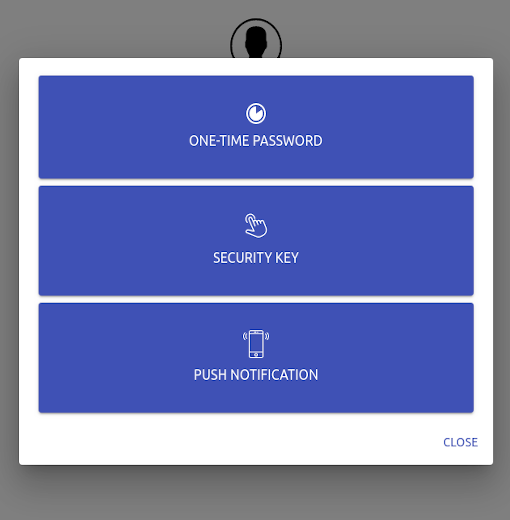
Here is what Authelia's portal looks like
Features summary
Here is the list of the main available features:
- Several kind of second factor:
- Password reset with identity verification using email confirmation.
- Single-factor only authentication method available.
- Access restriction after too many authentication attempts.
- Fine-grained access control per subdomain, user, resource and network.
- Support of basic authentication for endpoints protected by single factor.
- Highly available using a remote database and Redis as a highly available KV store.
- Compatible with Kubernetes ingress-nginx controller out of the box.
For more details about the features, follow Features.
If you want to know more about the roadmap, follow Roadmap.
Proxy support
Authelia works in combination with nginx, Traefik or HAProxy. It can be deployed on bare metal with Docker or on top of Kubernetes.




Getting Started
You can start utilising Authelia with the provided docker-compose bundles:
Local
The Local compose bundle is intended to test Authelia without worrying about configuration. It's meant to be used for scenarios where the server is not be exposed to the internet. Domains will be defined in the local hosts file and self-signed certificates will be utilised.
Lite
The Lite compose bundle is intended for scenarios where the server will be exposed to the internet, domains and DNS will need to be setup accordingly and certificates will be generated through LetsEncrypt. The Lite element refers to minimal external dependencies; File based user storage, SQLite based configuration storage. In this configuration, the service will not scale well.
Full
The Full compose bundle is intended for scenarios where the server will be exposed to the internet, domains and DNS will need to be setup accordingly and certificates will be generated through LetsEncrypt. The Full element refers to a scalable setup which includes external dependencies; LDAP based user storage, Database based configuration storage (MariaDB, MySQL or Postgres).
Deployment
Now that you have tested Authelia and you want to try it out in your own infrastructure, you can learn how to deploy and use it with Deployment. This guide will show you how to deploy it on bare metal as well as on Kubernetes.
Security
Authelia takes security very seriously. We follow the rule of responsible disclosure, and we encourage the community to as well.
If you discover a vulnerability in Authelia, please first contact one of the maintainers privately either via Matrix or email as described in the contact options below.
For details about security measures implemented in Authelia, please follow this link and for reading about the threat model follow this link.
Contact Options
Matrix
Join the Matrix Room and locate one of the maintainers. You can identify them as they are the room administrators. Alternatively you can just ask for one of the maintainers. Once you've made contact we ask you privately message the maintainer to communicate the vulnerability.
You can contact any of the maintainers for security vulnerability related issues by emailing security@authelia.com. This email is strictly reserved for security and vulnerability disclosure related matters. If you need to contact us for another reason please use Matrix or team@authelia.com.
Breaking changes
See BREAKING.
Contribute
If you want to contribute to Authelia, check the documentation available here.
Contributors
Authelia exists thanks to all the people who contribute. [Contribute].
Backers
Thank you to all our backers! 🙏 [Become a backer] and help us sustain our community.
Sponsors
Support Authelia by becoming a sponsor. Your logo will show up here with a link to your website. [Become a sponsor]
License
Authelia is licensed under the Apache 2.0 license. The terms of the license are detailed in LICENSE.









