* Add period TOPT config key to define the time in seconds each OTP is rotated * Add skew TOTP config to define how many keys either side of the current one should be considered valid * Add tests and set minimum values * Update config template * Use unix epoch for position calculation and Fix QR gen * This resolves the timer resetting improperly at the 0 seconds mark and allows for periods longer than 1 minute * Generate QR based on period * Fix OTP timer graphic |
||
|---|---|---|
| .buildkite | ||
| .dependabot | ||
| .github | ||
| cmd | ||
| docs | ||
| internal | ||
| web | ||
| .dockerignore | ||
| .gitignore | ||
| BREAKING.md | ||
| CONTRIBUTING.md | ||
| Dockerfile | ||
| Dockerfile.arm32v7 | ||
| Dockerfile.arm64v8 | ||
| LICENSE | ||
| README.md | ||
| authelia.service | ||
| bootstrap.sh | ||
| config.template.yml | ||
| go.mod | ||
| go.sum | ||
README.md

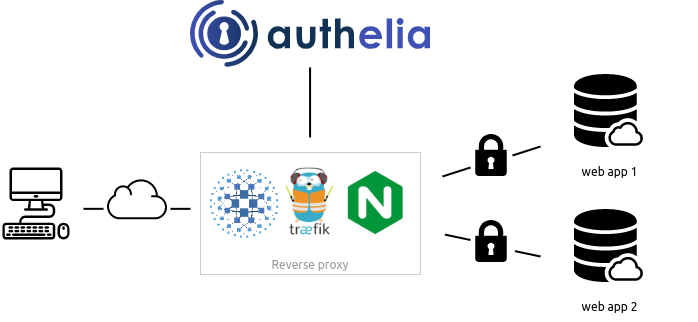
Authelia is an open-source authentication and authorization server providing 2-factor authentication and single sign-on (SSO) for your applications via a web portal. It acts as a companion of reverse proxies like nginx, Traefik or HAProxy to let them know whether queries should pass through. Unauthenticated user are redirected to Authelia Sign-in portal instead.
Documentation is available at https://docs.authelia.com.
The architecture is shown in the diagram below.
BREAKING NEWS: Authelia v4 has been released! Please read BREAKING.md if you want to migrate from v3 to v4. Otherwise, start fresh in v4 and enjoy!
Authelia can be installed as a standalone service from the AUR, using a Static binary, Docker or can also be deployed easily on Kubernetes leveraging ingress controllers and ingress configuration.

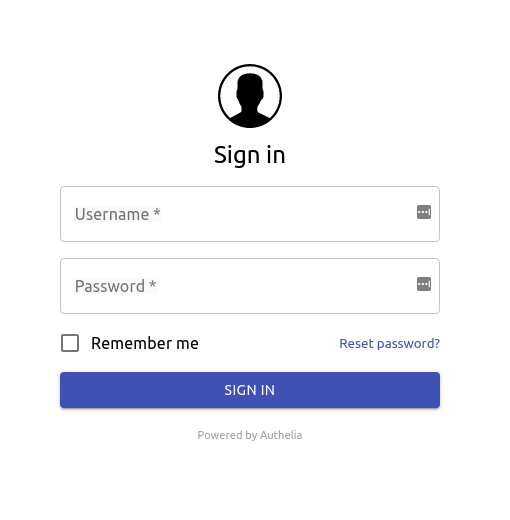
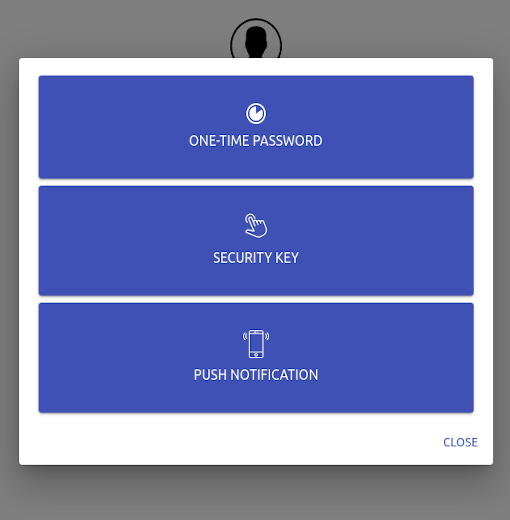
Here is what Authelia's portal looks like
Features summary
Here is the list of the main available features:
- Several kind of second factor:
- Password reset with identity verification using email confirmation.
- Single-factor only authentication method available.
- Access restriction after too many authentication attempts.
- Fine-grained access control per subdomain, user, resource and network.
- Support of basic authentication for endpoints protected by single factor.
- Highly available using a remote database and Redis as a highly available KV store.
- Compatible with Kubernetes ingress-nginx controller out of the box.
For more details about the features, follow Features.
Proxy support
Authelia works in combination with nginx, Traefik or HAProxy. It can be deployed on bare metal with Docker or on top of Kubernetes.




Getting Started
You can start off with
git clone https://github.com/authelia/authelia.git && cd authelia
source bootstrap.sh
If you want to go further, please read Getting Started.
Deployment
Now that you have tested Authelia and you want to try it out in your own infrastructure, you can learn how to deploy and use it with Deployment. This guide will show you how to deploy it on bare metal as well as on Kubernetes.
Security
Security is taken very seriously here, therefore we follow the rule of responsible disclosure and we encourage you to do so.
Would you like to report any vulnerability discovered in Authelia, please first contact clems4ever on Matrix or by email.
For details about security measures implemented in Authelia, please follow this link.
Breaking changes
See BREAKING.
Contribute
If you want to contribute to Authelia, check the documentation available here.
Sponsorship
Become a backer to support Authelia.
License
Authelia is licensed under the Apache 2.0 license. The terms of the license are detailed in LICENSE.









